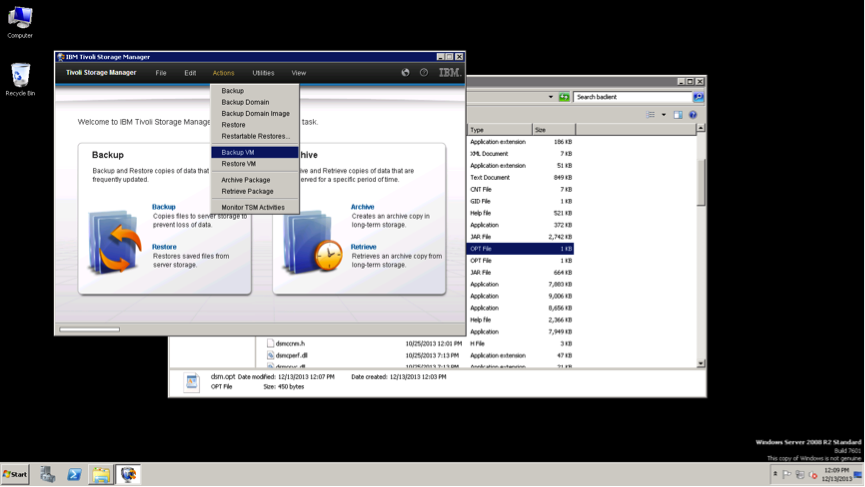
During backup processing, the application server was not notified that the backup to the Tivoli Storage Manager server completed successfully. As a result, logs were not truncated on the application server. Data Protection for VMware V7.1 backs up VM guests with both guest level application consistency and log truncation which is not available in previous versions. You can back up these VM guests with the following interfaces
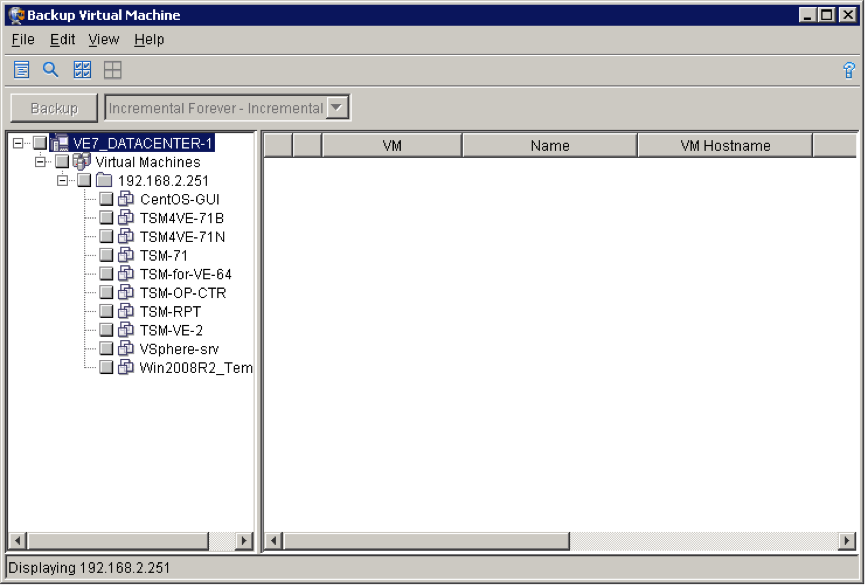
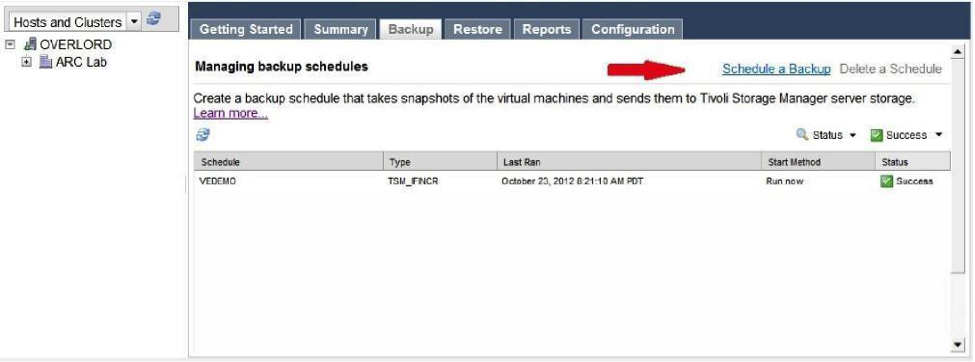
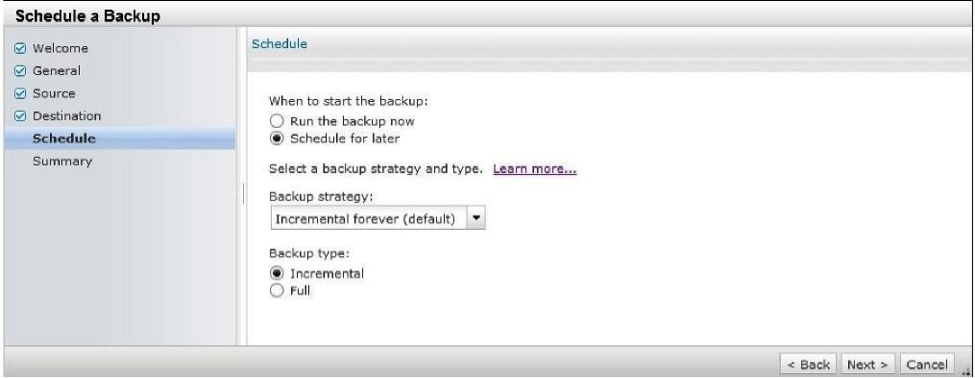
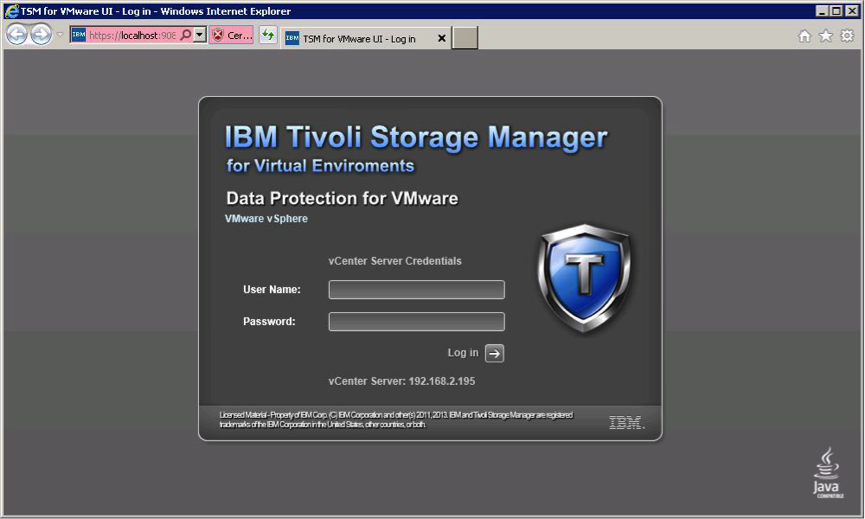
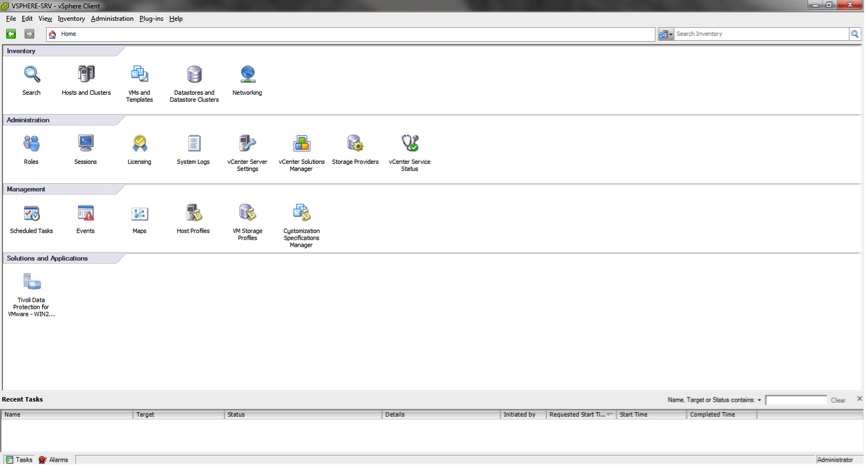
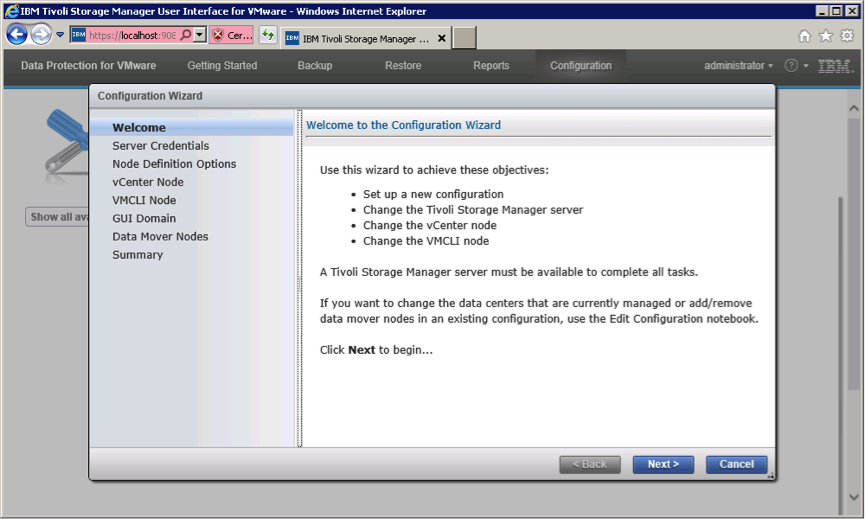
- Data Protection for VMware vSphere GUI
- Tivoli Storage Manager backup-archive client command-line interface
- Tivoli Storage Manager backup-archive client Web client
- Tivoli Storage Manager backup-archive client GUI based on Oracle Java
Choosing the protection type for database & applications inside the VM's
- Off-host data protection solutions that feature a backup/recovery agent that can be hosted on a machine other than the hypervisor host, for example, Tivoli Storage Manager for Virtual Environments (Data Protection for VMware) and Tivoli Storage FlashCopy Manager for VMware.
- In-guest data protection solutions that require the deployment of a backup/recovery agent in the guest machine, for example, Tivoli Storage Manager for Mail (Data Protection for Microsoft Exchange Server) or Tivoli Storage Manager for Databases (Data Protection for Microsoft SQL Server).
- Hybrid solutions that use elements of both off-host data protection and in-guest data protection solutions.
- Recovery time objectives (RTO) - block-level recovery from an off-host backup may give shorter recovery time as compared to recovery from an in-guest backup.
- Recovery point objectives (RPO) - recovery of transaction logs produced by in-guest backup may minimize data loss in a recovery scenario.
- Type of storage - raw device mapping disks in physical compatibility mode cannot be the target of a VMware snapshot operation and would be better suited for in-guest solutions.
- Other considerations including storage vendor, data layout, Tivoli Storage Manager server configuration, long-term recovery requirements, and so on.
- Raw device mapped volumes created in physical compatibility mode (pRDM)
- Independent disks
- iSCSI disks attached directly to the virtual machine
Protecting Microsoft SQL Server database inside the VM
- Microsoft SQL Server database files are already stored on disks that can be protected by virtual machine snapshots.
- Not having AlwaysOn Availability Groups, AlwaysOn Failover Clusters, or SQL servers deployed in cluster configurations.
- No requirement to recover to any specified point in time and databases are configured in simple recovery mode.
- SQL databases are configured in full recovery mode but log roll-forward is not a requirement.
- No need to recover individual databases or already protecting Microsoft SQL Server database in some other way.
- If you can use a global policy on a per-virtual machine or per-datastore basis to manage retention of Microsoft SQL Server data
- If you have Microsoft SQL Server database files stored on disks that can be protected by virtual machine snapshots.
- If you don't have AlwaysOn Availability Groups, AlwaysOn Failover Clusters, or SQL servers deployed in cluster configurations.
- If you need to recover individual databases without disrupting other databases on the same server.
- If you need to recover to any specified point in time using transaction logs
- If you have Microsoft SQL Server databases deployed on physical compatibility raw device mapped (pRDM), independent, or direct iSCSI mounted disks.
- If you have AlwaysOn Availability Groups, AlwaysOn Failover Clusters, or Microsoft SQL Server deployed in a cluster configuration.
- If you need to define policy at an individual database level
Protecting Microsoft Exchange Mail Server inside the VM
- If you have Microsoft Exchange Server database files stored on disks that can be protected by virtual machine snapshots.
- If you don't need to recover an individual database.
- If you can use a global policy on a per-virtual machine or per-datastore basis to manage retention of Microsoft Exchange Server data.
- If you are using native Microsoft Exchange Server features to satisfy individual mailbox/mailbox message recovery or you do not need to recover individual mailbox/mailbox messages.
- If you do not have any special recovery point objective requirements that would necessitate log recovery or if you are using continuous replication circular logging.
- If you need to be able to recover an entire virtual machine to rebuild a Microsoft Exchange Server configured in a database availability group.
- If you have Microsoft Exchange Server database files stored on disks that can be protected by virtual machine snapshots.
- If you have no special recovery point objective requirements that would necessitate log recovery or you are using continuous replication circular logging.
- If you can use a global policy on a per-virtual machine basis to manage retention of Microsoft Exchange Server data and any of the following conditions are met.
- If you need to perform frequent individual mailbox or mailbox item recovery operations and concerned with recovery time objectives.
- If you need to be able to recover an entire virtual machine to rebuild a Microsoft Exchange Server configured in a database availability group.
- Recovery of individual databases and/or servers can be coordinated with other resources (for example, for clustered servers or database availability group configurations).
- Recovery to specific point-in-time states based on log recovery can be achieved to satisfy recovery point objective requirements.
- Mailbox and mailbox item recovery is integrated in the native in-guest agent interfaces
- Have Microsoft Exchange Server databases deployed on physical compatibility raw device mapped (pRDM), independent, or direct iSCSI mounted disksneed to perform frequent individual mailbox or mailbox item recovery operations.
- Have special recovery point objective requirements that would necessitate log recovery.
- Need to perform frequent recoveries of individual databases.
- Need to define policy at an individual database level
Protecting File/web/print server/workstation (unstructured data)
Off-host solutions such as Data Protection for VMware are well suited for most backup and recovery use cases as they provide efficient block-level, incremental backups to reduce the steady-state backup windows and provide administrators with the ability to perform recoveries of the entire virtual machine or recoveries of only specific files and directories.
In-guest agents need to be used in situations where disks cannot be protected by off-host solutions (for example, physical raw device mapped volumes) or there are very specific recovery use cases.
Protecting Microsoft Active Directory
Microsoft and VMware have provided built-in tools to facilitate recovery and replication with Windows Server 2012. Prior versions of Windows Server required explicit changes in the data protection products in order to ensure that Active Directory replication was aware when a machine was being recovered to a site with at least one pre-existing domain controller.
Protecting Other applications
If you are using any other applications other than the above discussed applications, it is recommended to use In-guest data protection software to protect them. For example- If you are using Lotus Domino, SAP ERP or Oracle Databases within the VM's, it is recommended to use In-guest data protection (TDP Domino, TDP Oracle etc.) to protect the application data.
- If you are using DB2 database, you can use only BA Client to configure the backup to TSM server.